|
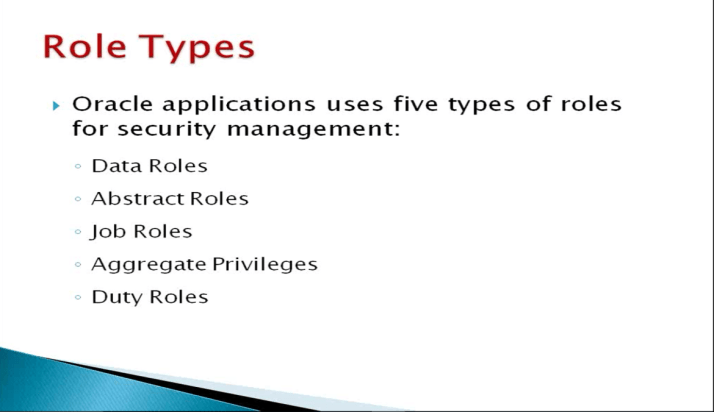
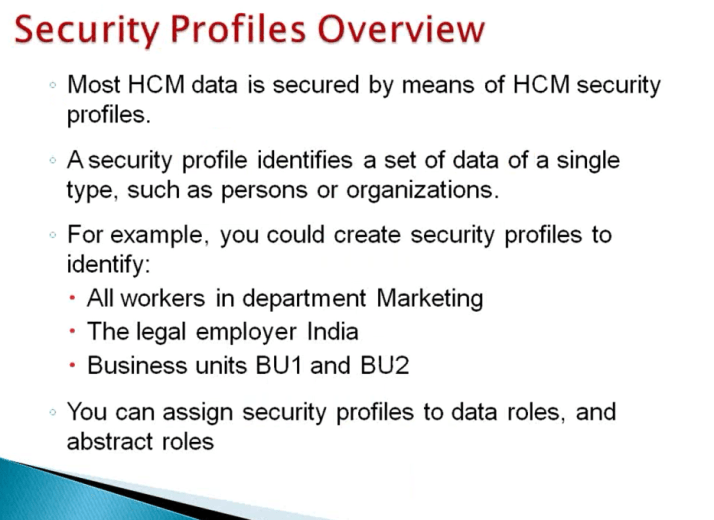
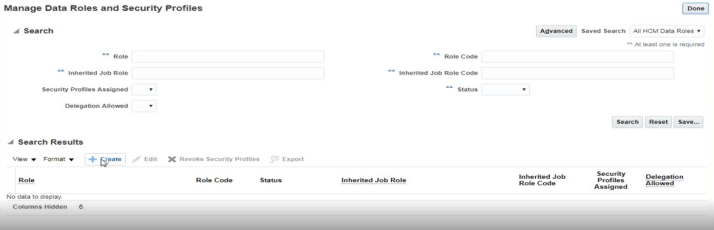
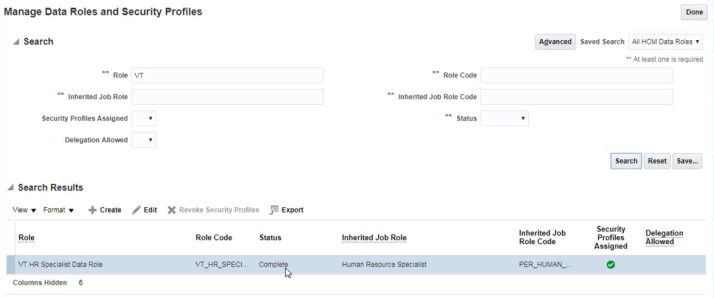
Data Roles:
- Data role is combination of Function Security and Data Security.
- In other words it is combination of workers job and the data instances that user with this role need to access.
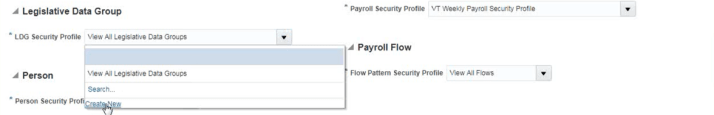
- Function Security: When user login to instance what function or task user can perform and to perform those activities what user interfaces he need access to.
- Data Security: Once user gets into particular user interface then data security determines what legal entity, job, grades, organizations and people information user has access to.
- These Data Roles needs to be created and assigned to user, through these Data Roles user get access to Function Security and Data Security.
|
|
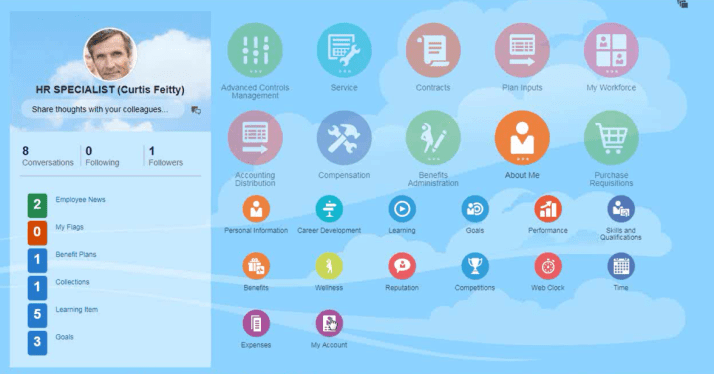
Abstract Roles:
- There are only 3 abstract roles and those are
- Employee
- Line Manager
- Contingent Worker
- We can assign these roles to employee and contingent worker and abstract roles giver access to self service pages (employee, line manager, Contingent) and they can perform only activities related to self service. In other words they can perform any activity with respect to business.
- For example if we want employee to perform payroll administrator and if we only give him Employee abstract role then he will not be able to perform payroll administrator role until we give him payroll administrator data role.
- In nutshell we hire a person to perform certain activities and alone Abstract role will not meet any purpose and we need to assigned user a required Data Role to perform those activities.
- Bare minimum user must have access to 1 Abstract Role and 1 Data Role.
|
|
|
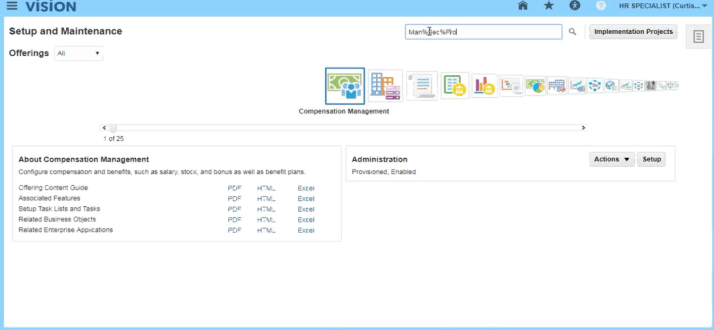
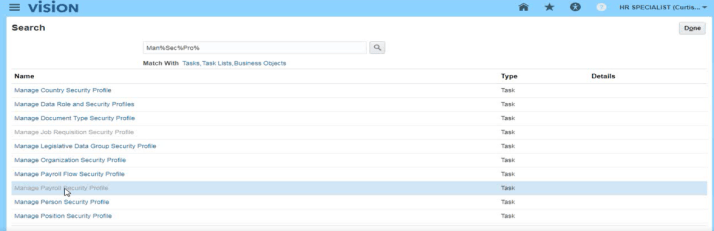
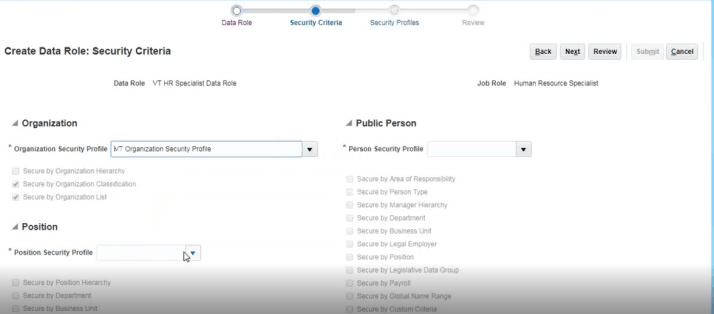
Job Roles, Duty Roles and Aggregate Privileges:
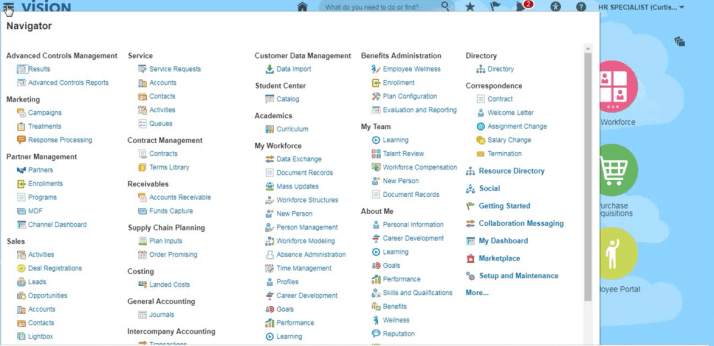
- Functional Security part of Data Role is controlled by Job Role, Aggregate Privileges and Duty Roles.
- Job role will give access to specific activities. For example payroll administrator is a Job Role.
- For example HR Specialist is a job role, being HR specialist he will be able to perform HR specialist related activities.
- Job role will give what activities will be perform by user thereby the functional security part is controlled.
- Alone Job role will not be sufficient for example if we created a person with HR specialist job role, a HR specialist can hire people, transfer people, can promote people, can terminate people so as it gives full access to person where as we only want to give him access to hire and terminate people and should NOT promote or transfer people. In this case Duty role and Aggregate
Privilege can help.
|